When people talk about early cyber warfare, Stuxnet usually takes center stage. It’s often described as the first true digital weapon—precision-engineered to sabotage Iran’s nuclear program.
But new research from SentinelOne suggests something even more intriguing:
Stuxnet may not have been the first.
A Weapon Ahead of Its Time
Recently uncovered references to a component called fast16.sys point to a highly targeted cyber operation dating back to around 2005—roughly five years before Stuxnet made headlines.
This earlier tool appears to have been designed with a similar strategic goal: sabotaging highly specific engineering software environments, likely tied to industrial or nuclear development workflows.
What makes it remarkable isn’t just when it existed—but how it operated.
Stealth on Another Level
Unlike traditional malware—even by modern standards—this cyber weapon avoided leaving obvious traces on disk. Instead, it:
- Intercepted files only during loading and execution
- Modified behavior in memory, not on disk
- Left original files untouched, making forensic detection extremely difficult
In practical terms, this means systems could appear completely clean—even while being actively manipulated.
If Stuxnet was a guided missile, this was more like a ghost in the machinery.
Precision Targeting
Evidence suggests the tool wasn’t broadly deployed. It was:
- Highly selective
- Likely activated only under very specific conditions
- Designed to interact with niche engineering or industrial software
That level of targeting strongly indicates a state-sponsored operation, rather than cybercrime or opportunistic espionage.
Why We’re Only Hearing About It Now
The most fascinating part?
This capability appears to have gone unnoticed for nearly two decades.
Because it didn’t rely on traditional infection techniques—and didn’t leave behind typical artifacts—it effectively slipped under the radar of both defenders and researchers.
Only through retrospective analysis of leaked tooling references (including links to the Shadow Brokers disclosures) did this piece of history come into focus.
Rethinking Cyber Warfare History
If these findings hold, they reshape the timeline:
- Advanced cyber sabotage capabilities existed earlier than previously believed
- Techniques like fileless execution and in-memory manipulation were in use long before they became mainstream threats
- Stuxnet may have been less of a beginning—and more of a public reveal of an already mature capability
Final Thoughts
There’s something almost unsettling about this discovery.
Not just because of what it did—but because of how long it remained invisible.
It raises a simple question:
How many other “ghost tools” are still out there, waiting to be discovered?
(And somewhere, HAL 9000 would calmly say: “I’m sorry, Dave… I’ve been here the whole time.”)
Original full article here;
https://www.sentinelone.com/labs/fast16-mystery-shadowbrokers-reference-reveals-high-precision-software-sabotage-5-years-before-stuxnet
Have you ever wondered, “Is this really a scam, or am I just incredibly lucky and about to inherit $10 million from an uncle I never heard of?”
If so, give Scamio a try! It’s a free AI chatbot that you can consult about suspicious emails, SMS messages, websites, and more.
It’s free and easy to use!
Bitdefender Scamio – Free Scam Detector

Are you using WinRar? well in that case you may want to update. A security flaw has been found in WinRar that could allow malicious code to execute just by opening a WinRar file (nasty)..


Read much more on Bleeping Computers . Com
https://www.rarlab.com/rarnew.htm
Download update here;
Quad9 the free secure DNS service is in trouble and need our help.
https://www.quad9.net/letter-of-support-for-quad9-and-freedom-of-dns-resolution/
Explainer
If you dont know what Quad9 is, then here is a short explainer. Quad9 is a free DNS services much like Googles well known 8.8.8.8 and 8.8.4.4, Quad9 (9.9.9.9 and 149.112.112.112) however add a very cool FREE security layer to the solution (a bit like Ciscos Umbrella, just not quite as customizable). If you use Quad9s DNS as your DNS service and you get infected by malware (eg. ransomware etc.) then chances are that the malware will try to “phone home” to its command and control server – Quad9 will blocks communication to known command and control DNS addresses thus disrupting many botnets or ransomware “providers”.
Anyhow, Sony has in Germany started a court case to force Quad9 to censor DNS resolution, Sony want Quad9 to block access to pages that Sony claim contain copyright protected content. In Denmark (where I live) we have a similar DNS blocking mandatory for national DNS services, it was originally introduced to block access to child phonography (something all of us could support) – but quickly the music industry and other rights owners/lobbyists saw this as a golden opportunity to block whatever they did not like and succeeded in convincing courts to add to the blocklist.
I support working against crime and child phonography however I do not think DNS blocking is the solution (perhaps against terrorism, pedophilia and violent crimes – but not for immaterial rights), experiences have shown, that what starts as a noble initiative quickly become a tool for lobbyists and huge enterprises to suppress whatever they dont like on the internet.
In general I think that more police, and more crossborder police collaboration is the way forth – not letting Sony and other dictate what is on the internet.
I supported the DNS blocking back in the days when the goal was to protect children against misuse, but now when it is a tool for mega companies and lobbyists my respect is gone.
Did you know:
Quad 9 offers free DNS services with malware filtering – to use just set your DNS (and or DNS servers) to query 9.9.9.9 and 149.112.112.112, then block all other DNS traffic outbound and presto you added a free additional security layer to your setup (company or personal). It is important to add the blocking for other DNS queries in your firewall as malware otherwise could easily bypass your protection. Read more here: https://www.quad9.net/service/service-addresses-and-features
Backblaze has something similar – here you use 1.1.1.2 (blocks malware like Quad9) and 1.1.1.3 (blocks both malware and pornography).
Read more here; https://blog.cloudflare.com/introducing-1-1-1-1-for-families/
To whom it may concern:
We believe that the act of recursive DNS resolution is not within the justifiable legal boundaries of control by rightsholders during infringement litigation. In order for the DNS to remain a stable, secure, and trusted platform, we would urge policymakers and regulators to clarify and reiterate the long-standing understanding that recursive resolution is a neutral technical function that should not be subject to blocking demands imposed by private parties based on data that has not been ruled upon by a suitable and fair court process.
Further, we believe that systems that are designed for providing cybersecurity (be they DNS-based or otherwise) should not be made available to be repurposed for other goals against the interest and intent of the service operator or the end user. This type of corruption of core internet infrastructure risks eroding the trust in both the operators and a technology that is core to the continued well-being of the internet and that of the citizens who use it.
We support Quad9 in their objection to the ruling of the Hamburg Court of (Case 310 O 99/21), and hope that the court finds in favor of the defendant.
Bad news for the Windows server admins, it would appear that at zero day exploit has surfaced that is extraordinary bad if you have Domain Controllers with the print-spooler service running (eg. printer role). The exploit allow an attacker to execute code as system via a normal domain user account. As of this post there is no patch available.
Potential Mitigation
Stop and disable the “Printer Spooler” service on servers where it is not required (especially DC’s).
Read more here: https://msrc.microsoft.com/update-guide/en-US/vulnerability/CVE-2021-1675


Do you use Cisco AnyConnect VPN? You may want to check up on your build :-O you need at least Release 4.9.00086
Download fixed build here;
https://software.cisco.com/download/home/286281283/type/282364313/release/4.9.00086

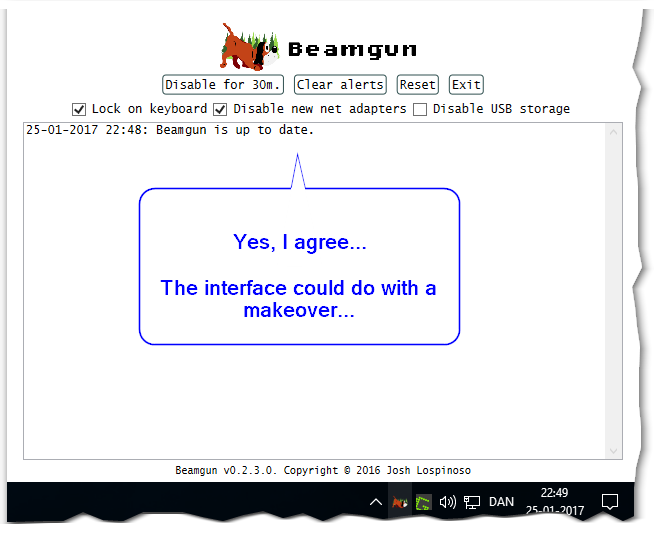
 BeamGun – So what is it all about, and do I need it?
BeamGun – So what is it all about, and do I need it?
Well, to answer the latter first – “maybe”, if you could ever see yourself inserting a USB key you found somewhere, or if other people have access to your computer….
Background;
All modern computers have USB ports, you can attach all sorts of wonderful devices to USB ports – like mouse and keyboards, well imagine if someone made a device that looked like a USB key, however it actually emulated a keyboard – when you would plug this into your USB port it would tell your computer “Hey, I am totally a USB keyboard, honestly..”, and your computer would say “Hey that is cool, go ahead and be my second keyboard…”. So far so good, however, now this totally honest “keyboard” would start typing commands and your computer not knowing any better would think that it was you typing. So, long story short – any device looking like a USB key that is inserted into your computer has a chance to be an evil “Rubber Ducky USB” (that is the name under which many of these are actually sold), so someone either hands you a USB device and convince you to insert it (hey can you look at the report I just made) – or distracts you for a second and insert the USB device to your computer – BOOM and you are owned – in benign cases it just adds some practical joke (like switch your desktop background etc), but if evil it steals passwords etc. and it is very likely your Antivirus will not pick it up as it will look like commands issued from the local keyboard.
Sadly “no”, this is not Sci-Fi nor expensive, the script kiddie version of USB keys like this cost around 50$ but if you have real coding skills you can do it for 1-3$ 🙁
Ok, so anyone inserting a foreign USB device to your machine could be “hacking you”, or if you find an abandoned/lost USB key and insert it you may cause yourself to be hacked/compromised.
The tool;
https://github.com/JLospinoso/beamgun
BeamGun to the rescue – BeamGun is actually rather nifty, it will monitor your computer – and the moment a new “keyboard” (or something emulating a keyboard) is inserted, it will lock your computer and block the device, it will also show anything this device was trying to do in a popup window.
Mind you, it is an early version and seem a bit rough around the edges, but if you are in the “risk” group this may be a tool you would want to install. But it works (yes I tested it, however it is difficult to show screenshots as the software does a great job of protecting your computer while it display its warning).
Want to see more about these “Rubber Ducky USB” devices, take a look at this video;
https://youtu.be/4kX90HzA0FM
Something similar is also shown in the popular tv-show “Mr Robot”
Want to aspire as an evil hacker (or totally own your friends), buy your own “USB Rubber Ducky” here (yes its actually that simple);
https://hakshop.com/products/usb-rubber-ducky-deluxe
Links;
https://github.com/JLospinoso/beamgun
https://hakshop.com/products/usb-rubber-ducky-deluxe
 MDM or Mobile Device Management has become increasingly popular over the last few years. I was surprised to find, that when we implemented it in the company I work for we discovered that there actually was a few users without a pin or password on their mobile device (to be expected out of a few thousand users I guess, but still – NO PIN on your phone, REALLY!!!)!?
MDM or Mobile Device Management has become increasingly popular over the last few years. I was surprised to find, that when we implemented it in the company I work for we discovered that there actually was a few users without a pin or password on their mobile device (to be expected out of a few thousand users I guess, but still – NO PIN on your phone, REALLY!!!)!?
Anyhow, there are several reasons to dive into this area – AND the good news is that (depending on the size of your setup) you can actually do much for ZERO $ (Free).
Create Policies;
- Require that users (or family) have a PIN
- Deploy APPS to phones or tablets
- Keep track of installed APPS
- Create geo-fencing – be warned if the device leave a defined area (sadly this does not work well in Denmark as the matching of IP’s to addresses is very limited due to privacy legislation)
You can even choose to implement it in your household to keep track of what apps etc are installed be the kids etc.
So are there great skills required? no not really, perhaps a little in setting it up initially – and there are some minor challenges, especially with the certificate part (which need to maintained/updated yearly), but in general – if you have experience with IT operations it’s more or less a breeze.
To get started here are a few links.
Several free or cheap services exist, to name a few;
The first one “Meraki” I actually tried and is still using (free for up to 100 devices as I recall)
https://account.meraki.com/login/new_account
You can even get a free cloud managed WiFi Access Point if you attend one of their online seminars.
Additionally you can install Windows Clients on Windows PC’s and thus now also have free inventory of your Windows PC’s.
You can see a demo of a related Meraki mobile management pack, it’s not quite the same as the free MDM solution – but it can give you some idea of what is possible.
https://youtu.be/fa95GJZQ0fQ
Another one is Spiceworks, I have not tried their MDM solution – but the “Spiceworks framework” (free IT operations software) in general is quite good and capable.
https://www.spiceworks.com/free-mobile-device-management-mdm-software/