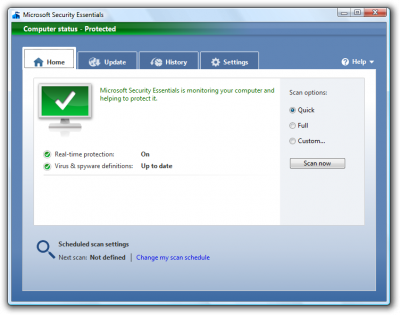
 Yes it is here “Microsoft Security Essentials”, the Beta for Microsoft’s new free anti virus (previously codenamed morro) and the replacement for One Care Live a paid anti virus solution Microsoft attempted earlier which reached eol in June 2009.
Yes it is here “Microsoft Security Essentials”, the Beta for Microsoft’s new free anti virus (previously codenamed morro) and the replacement for One Care Live a paid anti virus solution Microsoft attempted earlier which reached eol in June 2009.
We use Forefront Client Security (Microsoft’s corporate anti virus solution) at work, and it works quite well. The malware and anti virus part is just as good as any I have tried, but the corporate management part is somewhat lagging I would say. But as Microsoft Security Essentials is a standalone product this is not an issue, and I would suspect the engine etc. to be the same as Forefront Client Security so all in all I expect this to be an excelent product.
Read more;
http://www.microsoft.com/security_essentials/
Here you can also get the beta (if you are eligible)
http://hacktolive.org/wiki/Microsoft_Security_Essentials
Here you can also get the beta (if you are not eligible 😉 )
A pretty good walkthrough here;
http://www.winsupersite.com/win7/mse_beta.asp
Some random posts;
http://www.addictivetips.com/windows-tips/microsoft-security-essentials-review-with-screenshots/
http://www.pcworld.com/article/167160/is_microsofts_morro_malware_in_disguise.html


