Have you ever tried enabling Shadow Copy on a server drive? Shadow Copy (in this “Shared folders” variant) is a poor man’s backup/version control, it will allow you to restore previous versions of files deleted via shares.
Technical info on how it works;
http://technet.microsoft.com/en-us/library/cc785914(WS.10).aspx
A more lo tech approach here (visual demo);
http://www.microsoft.com/windowsserver2003/docs/ShadowCopiesSharedFolders.swf
http://www.microsoft.com/windowsserver2003/techinfo/overview/scr.mspx
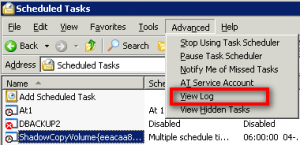
Image1
Anyhow, once implemented Shadow Copy will begin to “backup” data via a Scheduled Job if you so choose (the scheduled job is added to the scheduled tasks in the control panel automatically).
However, when I looked in the logfile for scheduled jobs (see image1) there was mention of an error (which is odd as the schedule is created by the system and as such should be correct);
.
"ShadowCopyVolume{eeacaa88-d521-11da-a3c1-00170859ede5}.job" (vssadmin.exe)
31-08-2009 12:00:00 ** WARNING ** Invalid working directory..
The specific error is: 0x00000003: The system cannot find the path specified.
Now this was odd because the Shadow Copy backup worked without a glitch and files could be restored, so why the error!? Well a bit of digging around brought me a step closer to the truth, but sadly not all the way (I now know how to fix it, but not why the errormessage appears)..
It would appear that the error is related to the “Working directory” in the scheduled task, and the suggestion was to clear the “Working directory” field in the scheduled job – does it make sense? well not really, working directory pointed at “%systemroot%\system32” which equals “C:\windows\system32” and this folder DO exist but never the less it did the trick – no more errors in the SchedLgU.txt file.
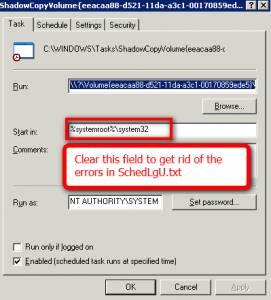 So the task is easy, simply delete the folder “working folder” in the scheduled job, normally called “ShadowCopyVolume{……….” and the errors are gone. Is this really nessesary? Nope, not at all it’s purely cosmetic, the job works even with the error message, so it’s only if you get annoyed by error messages in you log files.
So the task is easy, simply delete the folder “working folder” in the scheduled job, normally called “ShadowCopyVolume{……….” and the errors are gone. Is this really nessesary? Nope, not at all it’s purely cosmetic, the job works even with the error message, so it’s only if you get annoyed by error messages in you log files.
.

 Need to repartition your harddisk? Don’t want to pay hundreds of dollars for Partition Magic?
Need to repartition your harddisk? Don’t want to pay hundreds of dollars for Partition Magic?

 I looked for this for ages, but at some point I got my google search right and this is what it turned out;
I looked for this for ages, but at some point I got my google search right and this is what it turned out;
 But now there is a new player on the marked,
But now there is a new player on the marked,